This was yet another significant week in ElastOS history. In seven days, the team shipped 18 commits touching 102 core files, adding roughly 10,000 lines of code, releasing the ElastOS Runtime publicly for the first time, connecting production-grade digital rights management, proving that third-party apps can run inside the system, and launching a unified documentation portal at docs.elastos.net.
What Shipped: The Big Picture
Nine major systems went from development to working product in a single sprint:
- ElastOS Runtime v0.1.0, Public Release, the core execution engine that makes software unable to betray its users, released publicly on GitHub for the first time
- Runtime Engineering, Chat, Security, and WCI Exec Room, three fundamental communication bugs fixed, ten security vulnerabilities closed, and a live collaboration room built
- Particle Auth and Agent Wallet, users can now log in with email or Google and have a wallet created automatically, with no MetaMask required
- Lit Protocol Production Integration, real digital rights management is live on mainnet for the first time, protecting real content with real money
- Free Content Minting, creators can now publish free content with on-chain attribution, no encryption overhead
- Glide Finance DEX, the first third-party application running inside the system, proving it is a platform and not just a product
- Capsule-Compatible Refactoring, production code restructured to slot directly into the next-generation security architecture
- Documentation Portal, docs.elastos.net launched with guides covering all four core pillars
- Apple Developer Program, macOS distribution unblocked, meaning Mac users will soon be able to install ElastOS with a double-click
In parallel, ELA merge-mining launched on KuCoin’s KuMining platform, ecosystem identity issues were resolved, and the V3 Protocol SDK was built and documented.
1. ElastOS Runtime v0.1.0, The Operating System Kernel Goes Public
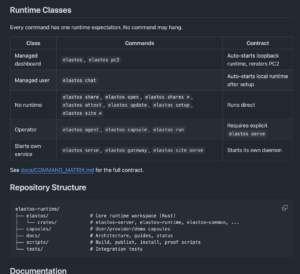
The ElastOS Runtime is the engine underneath everything. Think of it as the security guard, traffic controller, and building manager for your digital life, it decides which apps can run, what they can access, and ensures nothing happens without your permission. This week, for the first time, it was released publicly on GitHub as open-source software anyone can inspect, verify, and contribute to.
What does this mean in practice? One command installs it. You open a terminal, paste the install command, and within minutes you have a fully working personal computer environment where every application runs in its own sealed room. The system has been verified on Linux, NVIDIA Jetson (the small AI computers), and Windows Subsystem for Linux.
- v0.1.0 released April 1, v0.1.1 on April 2, a hidden dependency was removed and the Rust toolchain was pinned so builds are reproducible on any machine
- ~16,000 lines of Rust code, the codebase is written in Rust, a language designed for safety and performance, meaning entire classes of security bugs are impossible by design
- Five-capsule architecture, apps are isolated from each other like apartments in a building. One misbehaving app cannot access another’s data
2. Runtime Engineering, Fixing the Foundation
Before a public release can be credible, the foundation has to be rock solid. The team found and fixed three root causes that prevented different parts of the system from reliably talking to each other, development builds and production builds used different communication addresses, messages arrived faster than the system could register listeners, and reconnection after network interruptions silently failed.
- 10 security bugs fixed, three critical escape hatches removed from storage, provider, and namespace systems. These were ways an app could potentially access things outside its sealed room
- WCI Exec Room built, a live collaboration surface where multiple people can work together in real time. Think of it like Google Docs, but the document lives on your computer, not Google’s servers
- Control graph viewer rewritten, the entire codebase mapped as an interactive graph with 28 API endpoints and tests, making it possible to see how every piece connects to every other piece
3. Particle Auth, Log In with Email, Get a Wallet Automatically

Most people do not have MetaMask or know what a crypto wallet is. Particle Auth solves this by letting users log in with email, Google, or Apple, and automatically creating a wallet behind the scenes. The user never has to think about private keys, seed phrases, or browser extensions. They just log in the way they already know how. The security model is called MPC-TSS, which splits the private key across multiple parties so no single entity (not Particle, not your device, not the system) ever holds the complete key. Think of it like a safety deposit box that requires three different keys held by three different people, all three must agree before the box opens.
- Email users can send tokens, users who logged in with email can now send and receive tokens through a simple popup
- Agent Wallet, a full three-phase flow where the system creates a smart account, deposits initial funds, and executes operations on the user’s behalf
- Universal Account abstraction, works across multiple networks seamlessly, so the user does not need to think about which network they are on
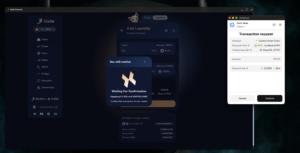
4. Elacity dDRM w/ Lit Protocol Production, Real Digital Rights Management Is Intergrated
Lit Protocol’s production network went live, and the team completed full integration into Elacity dDRM within 24 hours. The complete cycle works with real money on a real network: a creator uploads content, their system encrypts it, a buyer pays, and their system decrypts it, all verified end-to-end with every content type (PDF, image, video, and audio). This release will come in the upcoming ElastOS v1.2 release. This is the moment digital rights management became real and decentralised. No single company controls the encryption keys. No server can be shut down to revoke access. If you bought it, you own it, and the system enforces that mathematically, not through terms of service.
- Every format verified, PDF, image, video (DASH/CENC streaming), and audio all encrypt, mint, purchase, decrypt, and render correctly
- Cost: $0.01 per operation, session caching means multi-page PDFs cost one cent per session, not per page. Smart batching means five people buying the same item simultaneously share one decryption call
- 7 security vulnerabilities closed before going live, hardcoded endpoints replaced, token validation tightened, retry logic added for network interruptions
5. Free Content Minting, Not Everything Needs DRM
Not all content needs encryption. When a creator sets the price to zero, the system now skips the encryption step entirely. Content is packaged as a cleartext capsule with on-chain attribution, meaning the creator’s name is permanently recorded, but anyone can access the content freely. This lets creators offer free samples that drive traffic to paid work, publish open educational materials with permanent attribution, and distribute promotional content where the on-chain record proves who created it. Zero-price items cost only gas to mint and index an asset with a timestamp and provenance for all to watch and enjoy.
6. Glide Finance DEX, The First Third-Party App
If the system can only run apps the team builds, it is a product, not a platform. Glide Finance, the largest decentralised exchange on the Elastos network, now runs inside the system as a fully functional third-party application. Token swaps, liquidity management, farming, staking, analytics, and governance all work.
This proves the architecture is open enough for external developers to bring their own apps in, while still maintaining the security model. Two new software components were built alongside the integration: a multi-call encoder for batching multiple operations into one transaction, and an automated market maker engine for swap calculations.
- Smart caching delivers 38x speedup, frequently requested data (like which network you are on) is cached instead of fetched from the network every time
- 9 networks fully configured, Elastos, Ethereum, BSC, Polygon, Arbitrum, Optimism, Avalanche, Fantom, and Base, all with free public connection points
7. Capsule-Compatible Refactoring, Building for the Future Today
Rather than planning a future migration that never happens, the team restructured production code so it runs today while being designed to slot directly into the next-generation security architecture. Eight permission families were defined (file system, wallet, digital rights, compute, network, storage, identity, and agent). Every app now declares what it needs, and when the enforcement layer arrives, it will simply start checking those declarations.
- App signature verification, every app can now include a digital signature that proves the developer published it and nobody tampered with it
- Content integrity hashing, every protected file now includes a fingerprint so buyers can verify they received exactly what the creator uploaded
- 7 capsule manifests created, each software module now has a formal description of its permissions, dependencies, and capabilities
8. Documentation Portal, docs.elastos.net
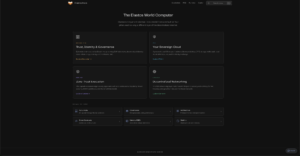
A unified documentation home launched at docs.elastos.net, covering all four core pillars: the main network, the personal computer environment, the Runtime engine, and the communication layer. Three audience paths guide different readers: builders who want to create apps, node operators who want to run infrastructure, and researchers exploring the architecture. The site includes AI compatibility (llms.txt) so developer tools can understand and reference the documentation automatically.
9. Apple Developer Program and KuMining Partnership
Apple accepted the Developer Program application, which unblocks code signing and notarisation for the Mac installer. This means Mac users will soon be able to download and install ElastOS with a double-click, no terminal commands, no security warnings, no technical knowledge required. Separately, ELA merge-mining launched on KuCoin’s KuMining platform. KuCoin is one of the top global exchanges, and having ELA mining accessible through their interface lowers the barrier for miners to participate in securing the Elastos network.
Website and Portal Updates
portal.ela.city
- New weekly development report added to the Proposal #212 dropdown with full detailed breakdown
- Monthly delivery summary updated, April spotlight now live with clickable monthly history
- Transaction transparency features expanded with new partner mappings and expense breakdowns
Elacity dDRM V3 Protocol
- SDK built with selectable v2/v3 protocol support for gradual migration
- CI/CD pipeline fixed and deployment completed
- Co-hosted documentation published
What’s Next
- ElastOS v1.2!
- Supernode deployment, deploy the Runtime to supernodes with production encryption configuration so the network runs on real infrastructure
- macOS installer, code-sign and notarise the Mac app so it installs with a double-click
- Large file encryption, test the pipeline with very large AI model files (4 to 70 gigabytes) using streaming encryption
- Decentralised relay, route encryption key requests through supernodes instead of a central server
- App Store UI, build the storefront with categories and search so users can discover and install third-party apps
- Conference circuit, representing ElastOS at Google Cloud Next, Bitcoin 2026, Consensus Miami, DAT Summit, and FT Digital Assets Summit across late-April and May
Try ElastOS
- Desktop Launcher (Mac and Linux): Download Launcher
- Terminal Install (Mac/Linux): curl -fsSL https://raw.githubusercontent.com/Elacity/pc2.net/main/scripts/start-local.sh | bash
- Runtime Install: curl -fsSL https://raw.githubusercontent.com/nicosql/elastos-runtime/main/scripts/install.sh | bash
- NVIDIA Jetson: cd ~ && git clone https://github.com/Elacity/pc2.net.git && cd pc2.net && sudo bash scripts/install-arm.sh
- Docs: docs.elastos.net | GitHub: github.com/Elacity/pc2.net
- Network Map: map.ela.city | Portal: portal.ela.city
- DAO Proposal: Keystone Fund Mandate
- Shipping Report: GitHub Discussion #9