The past two weeks have been the biggest building sprint in ElastOS history. From the tools creators use to upload, to the marketplace where buyers shop, to the security layer that prevents piracy, heres a look at whats being shipped behind the scenes.
What Shipped: The Big Picture
Seven major systems went from idea to working product:
- Elastos Runtime RC1/RC2 — the core engine that turns your hardware into a real personal computer is now working on Linux and Jetson devices, with apps that can safely talk to each other
- Supernode Decentralization Phase 2 — anyone can now help run the network’s infrastructure with a single command, and the system automatically finds and connects to the best available nodes
- 3D Network Map & Community Tools — a beautiful interactive globe showing every node in the network in real time, plus a developer toolkit with 47 automated tests
- Complete dDRM Creator-to-Consumer Pipeline — creators can now encrypt their work, list it for sale, and buyers can purchase and view it — all without a platform in the middle
- Lit Protocol Chipotle Migration — replaced a massive, complex security library with a single lightweight connection, making the whole system faster and future-proof
- WASM Security Runtime — when you view protected content, the original file never exists in your browser. You only see the rendered image or video — making piracy virtually impossible
- DASH/CENC Media Pipeline — DRM-protected video and music streaming that works everywhere, without needing special browser plugins like Netflix does
In parallel, the underlying rights management protocol was completely rewritten with 100% test coverage — meaning every single feature has been verified to work correctly.
1. Elastos Runtime RC1/RC2
The Elastos Runtime is the engine that makes your PC2 device an actual personal computer — not just a website you visit. It’s what lets apps run on your hardware, talk to each other securely, and connect to the wider network. This sprint it reached a major milestone:
- Working on Linux & Jetson — you can install apps, update them, chat, and connect to the network. It just works
- Clean architecture — the five core components (networking, web, app packaging, app running, and the node itself) are now cleanly separated, making it easier for developers to build on top of
- Apps can talk to each other safely — we proved that a native app and a sandboxed web app can send messages back and forth through a secure bridge. This is like two people speaking different languages but having a perfect real-time translator between them
- Permission system — apps can only access what you explicitly allow. No app can secretly read your files, use your network, or spy on other apps
The current focus is building chat apps that run in these secure sandboxes — proving that real, useful software can work within this trust model. This is what makes PC2 a genuine operating system. Third-party developers will be able to write apps that are powerful but can’t misbehave — they only get access to what you grant them.
2. Supernode Decentralization: Anyone Can Run Infrastructure

Supernodes are the backbone of the PC2 network — think of them like cell towers for the internet. They help your personal node find other nodes, relay content, and create encrypted tunnels so your data stays private. Until now, we ran all the supernodes. Phase 2 changes that:
- Gateway v2.0 — supernodes now talk to each other automatically, sharing information about who’s online and what’s available
- One-command setup — a single script (914 lines of automation) can turn a fresh server into a fully operational supernode. No manual configuration needed
- Network repair tool — a diagnostic script (481 lines) that automatically installs and configures all four layers of censorship-resistant networking
- Automatic discovery — your node checks multiple supernodes at once and remembers the best ones, so if one goes down, it switches instantly
- Relay mode — any PC2 user can flip a switch in Settings to help relay content for the network, strengthening it for everyone
- Supernode Manager app — a built-in dashboard to monitor your supernode’s health, what services it’s running, and network statistics
- Automatic failover — if a supernode goes offline, your encrypted tunnels automatically reconnect through another one. No interruption
- Economics plan — a strategy document outlining how supernode operators will eventually earn rewards for keeping the network running
A network owned by one company isn’t really decentralized. Phase 2 means anyone can run a supernode, the network finds them automatically, and if one disappears, traffic routes around it. This is how you build infrastructure that can’t be shut down.
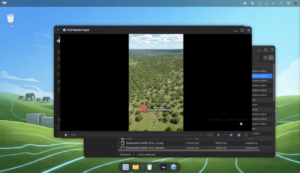
3D Network Visualization (map.ela.city):
- A beautiful interactive 3D globe showing every node in the ElastOS network, updated in real time
- Animated data flow — gold lines for the backbone, green for personal nodes, cyan for direct peer connections
- Different visual styles distinguish core infrastructure supernodes from community-run relay nodes
- Fully search-engine optimized so the network’s scale is visible to the world
3. Elacity dDRM: Your Content, Your Commerce
Imagine you’re a musician, photographer, or AI developer. Today, if you want to sell your work online, you go through a platform — Spotify, Shutterstock, or a marketplace — and they take 15-30% of every sale. They also control who sees your work, can change the rules anytime, and can remove your content without warning. Elacity dDRM flips this model. You encrypt your work, set your own price and royalty split, and sell it directly. Buyers get a cryptographic receipt (a token) proving they own access — not a permission slip that can be revoked. No middleman, no platform fees, no gatekeepers.
Creator Dashboard — Four Steps to Protected Content
A simple wizard that walks creators through protecting and selling their work:
- Pick your file — upload any digital content: images, PDFs, documents, music, video, code, AI models
- Describe it — add a title, description, category, and set your price
- Encrypt & upload — your file gets locked with military-grade encryption and stored on the decentralized IPFS network. Even if someone intercepts the file, they can’t open it without the key
- Publish for sale — your protected content is listed on the marketplace with automatic royalty splits built in (for example, 95% to you, 5% to the platform)
This was tested end-to-end with real money — real transactions, real payments in USDC, real content appearing in buyers’ libraries. Every PC2 node becomes both a storefront and a vault — your personal computer is your business.
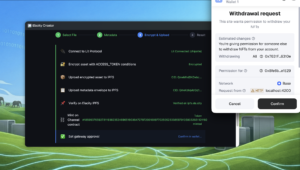
Market dApp — Browse, Buy, Own

The marketplace lets you browse what creators have listed, buy access with USDC (a dollar-pegged stablecoin), and see purchased content appear in your library instantly. We also fixed a confusing MetaMask popup that was scaring users during purchases — now the transaction details show up clearly.
Sovereign IPFS Pipeline

When you upload content, it goes to two places at once — your own PC2 node and Elacity’s distributed storage network. This means your files are never in the hands of a single company. If any one computer goes offline, your content is still available from the others. No Amazon S3, no Google Cloud — your infrastructure, your rules.
4. WASM Security Runtime: No Raw Files in Your Browser

Here’s the problem with most digital content protection: once you download a file to view it, you can copy it. Game over. Our solution: never let the raw file exist in your browser at all. When you open protected content, it goes through a secure pipeline:
- The encrypted file is fetched from storage
- It’s decrypted inside a sealed sandbox (think of it as an armored room inside your browser)
- The sandbox renders it as pixels on your screen — like taking a photo of a painting through a window
- The original file is immediately destroyed inside the sandbox
You see the image, read the PDF, or hear the music — but the original file never touches your browser where it could be copied. This is how Netflix protects its movies, but our version doesn’t need special browser plugins or hardware chips. It works everywhere. We built a dedicated dDRM Viewer app inside PC2 — complete with zoom, keyboard shortcuts, page navigation for documents, and audio playback. Protected content has a shield icon, and double-clicking opens it in the secure viewer. It feels like opening any normal file.
Security model: Encrypted file on IPFS → secure capsule on your device → double-click → dDRM Viewer → rights verified → decrypted and rendered as pixels → you see it. The raw file never exists outside the armored sandbox. All old pathways that could have leaked raw files were found and permanently removed.
5. DASH/CENC: Decentralized Netflix Without Browser Plugins
You can’t decrypt an entire 2GB movie before watching it — you’d be waiting forever. So instead, protected video gets split into tiny chunks, each encrypted separately. As you watch, each chunk is decrypted just before it plays, then discarded. This is how professional streaming services work — but ours is the first version that works without any browser plugins or special hardware. What we built:
- Video decryption engine — a custom-built tool that reads encrypted video chunks, decrypts them, strips the protection signaling, and feeds clean video to your player. The decryption keys live in a sealed sandbox and are erased after use
- Built-in video player — supports quality switching (like YouTube’s 720p/1080p selector), seeking, keyboard shortcuts, and music-only mode. No special browser extensions needed
- Server-side processing — the heavy lifting happens on your PC2 node, not in your browser. Your browser just receives clean, ready-to-play video. This means it works inside any web view, even restricted ones where Netflix and Spotify can’t operate
- Military-grade key exchange — the decryption key is never sent in the open. Instead, your node and the security service perform a cryptographic handshake (like two people creating a secret code only they understand) to safely pass the key
This is what makes decentralized Netflix and Spotify possible. Creators stream directly from their nodes. No central server, no 30% cut to Apple or Google, and it works on every device.
6. Lit Protocol Chipotle: Simpler, Faster, Future-Proof
Lit Protocol is our security partner — they hold the encryption keys for protected content inside tamper-proof hardware vaults and only release them when conditions are met (like verifying you actually purchased an asset). They’re upgrading their entire system (from “Datil” to “Chipotle”), and the old one shuts down in April 2026. We finished migrating before the deadline. What changed:
- Before: A massive library of code (~1.2MB), persistent connections, complex authentication ceremonies, and heavy browser dependencies that conflicted with our security sandboxes
- After: A single lightweight connection (~450 lines of code). One request in, one answer out. Simpler, faster, and works everywhere — including on servers and IoT devices, not just browsers
Important discovery: Content protected with the old system can’t be unlocked by the new one — they use completely different cryptography. So we built automatic detection: each piece of content remembers which system protected it, and the server sends it through the right pathway. Old content keeps working, new content uses the faster system. A single setting lets us switch back instantly if anything goes wrong. All security keys were removed from the source code, regenerated, and now live exclusively in secure, private configuration files.
7. ElacityLabs.com & Portal Overhaul

ElacityLabs.com got a major refresh
- A new animated visualization showing how dDRM works — from creator to buyer in six clear steps
- Full search engine optimization so people can discover ElastOS through Google
- Press coverage integrated — articles from CoinDesk, Yahoo Finance, TheStreet, Decential Media, and Chainwire
- Faster page loads — images converted to modern formats, loaded on demand instead of all at once
Portal.ela.city (the community dashboard) was redesigned:
- New Roadmap page — image carousel, news grid, live tweets, explore cards, development journal, and team section
- Proposal #212 tracker — a 36-month delivery tracker so the community can verify progress week by week
- Finance page — smooth animated tabs, faster data loading, and optimized code delivery
- Security improvements — sensitive data removed from code, environment-based configuration
- Mobile-friendly — navigation, tabs, and image layouts all work properly on phones now
What’s Next
- Video streaming upgrade — bring the new Chipotle security system to video and music streaming, and let users encode and stream video directly from their PC2 nodes
- Peer-to-peer trading — buy and sell content directly between nodes, no marketplace server needed
- AI Model Marketplace — sell and buy AI models as protected digital assets — download them to run locally on your own hardware
- Chat apps in sandboxes — real messaging apps running inside the secure capsule system, proving the permission model works for everyday software
- Cross-node sync — when you buy something on one node, every node in the network recognizes your ownership instantly
- Lit Datil deprecation — complete the transition to the new security system before the April 2026 deadline
- Community testing — open the Creator Dashboard to community members for real-world feedback
Try ElastOS
- Desktop Launcher (Mac & Linux): Download Launcher
- Terminal Install (Mac/Linux): curl -fsSL https://raw.githubusercontent.com/Elacity/pc2.net/main/scripts/start-local.sh | bash
- NVIDIA Jetson: cd ~ && git clone https://github.com/Elacity/pc2.net.git && cd pc2.net && sudo bash scripts/install-arm.sh
- Docs: docs.ela.city | GitHub: github.com/Elacity/pc2.net
- Network Map: map.ela.city | Portal: portal.ela.city
- DAO Proposal: Keystone Fund Mandate
- Shipping Report: GitHub Discussion #6