This was one of the most important weeks yet for the World Computer Initiative. Last week, the team shipped 53 commits across 434 files, covering security, Runtime, capsule packaging, supernode pinning, telemetry, and v1.2 release preparation.
The week focused on five major areas: the Runtime moving closer to a full desktop environment, the v1.2 launch surface taking shape, major security issues addresses across PC2 and the gateway, product and outreach progress, and the closure of a community-found P0 dDRM vulnerability.
The result is a release that is not only bigger, but also safer, more usable, and closer to what ElastOS is meant to become: a personal cloud computer where apps, identity, content, and user permissions belong to the user.
What Shipped: The Big Picture
- ElastOS Runtime moved closer to a real desktop environment, with a native desktop shell, hosted rooms, a GBA emulator, stronger capsule management, and a full Essentials codebase audit.
- The v1.2 launch surface took shape, with six signed and IPFS-pinned apps, supernode app-store support, a cleaner dApp Centre, telemetry plumbing, audio playback fixes, and UI polish.
- Security hardening shipped across PC2 and the gateway, closing all seven in-scope external researcher findings and 20 of 21 internal audit findings.
- Product, explorer, contracts, and outreach work moved forward, including Google Cloud Next, the live Elastos blockchain explorer, V3 contract ownership migration work, and continued enterprise conversations.
- A community-found P0 dDRM vulnerability was closed, with the new session-key delegation path verified across PDF, PNG, MP4, and MP3.
1. ElastOS Runtime Moves Toward a Real Desktop Environment
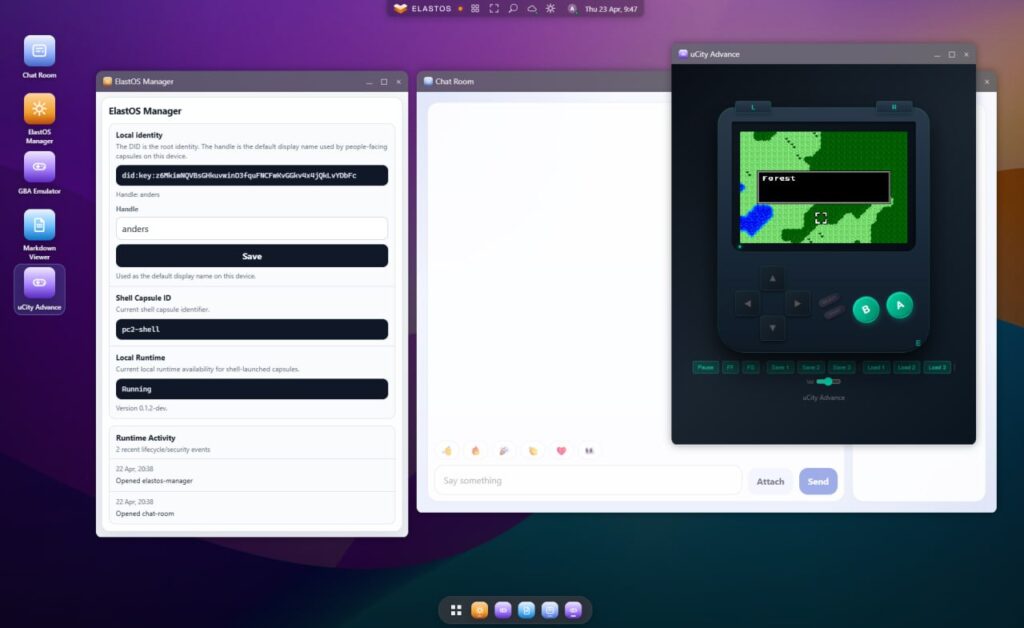
ElastOS Runtime is moving closer to the desktop environment that every PC2 capability can eventually plug into. This week, the Runtime started to feel less like a group of demos and more like a real operating environment.
The team advanced a native desktop shell built as a WASM capsule. It includes window management, a taskbar, search, a system tray, and an Elastos Manager control panel. The idea is simple: apps should run inside the Runtime through the same capsule model, instead of each part behaving like a separate system.
The hosted chat-room experience also moved forward. Users can now run rooms in two ways. In the first mode, each user runs the chat capsule on their own PC2 node and connects through Carrier. In the second mode, one node can host a public gateway page where external users request access, and the owner approves them from inside the Runtime.
A key principle remains that capsules talk through Carrier, while the Runtime controls what, if anything, becomes reachable from the public web. This keeps the capsule model focused on user control, while still allowing public access when the user chooses it.
The GBA emulator also improved this week. Save state now persists across reopens, and the emulator can detect other capsules nearby. That means different file types can open in the right place: a .gba file opens in the emulator, a markdown file opens in the viewer, and a video opens in the media player.
2. The v1.2 Launch Surface Takes Shape
With v1.2 getting close, the team used this week to make the release feel more complete for users, developers, and operators.
A new v1.2 adoption roadmap was published, with 1,082 lines mapping what needs to ship now, what comes next, and what can run in parallel. It covers the Runtime, the Capsule SDK, the dDRM protocol, and PC2, while tying each item to clear user outcomes.
The capsule packager also shipped. It packages app folders, computes a SHA-256 hash, signs the package with an Ed25519 key, uploads it to IPFS, and creates a registry entry. Six v1.2 apps were signed and pinned:
- Elacity Market
- Elacity Creator
- Elacity Player
- dDRM Viewer
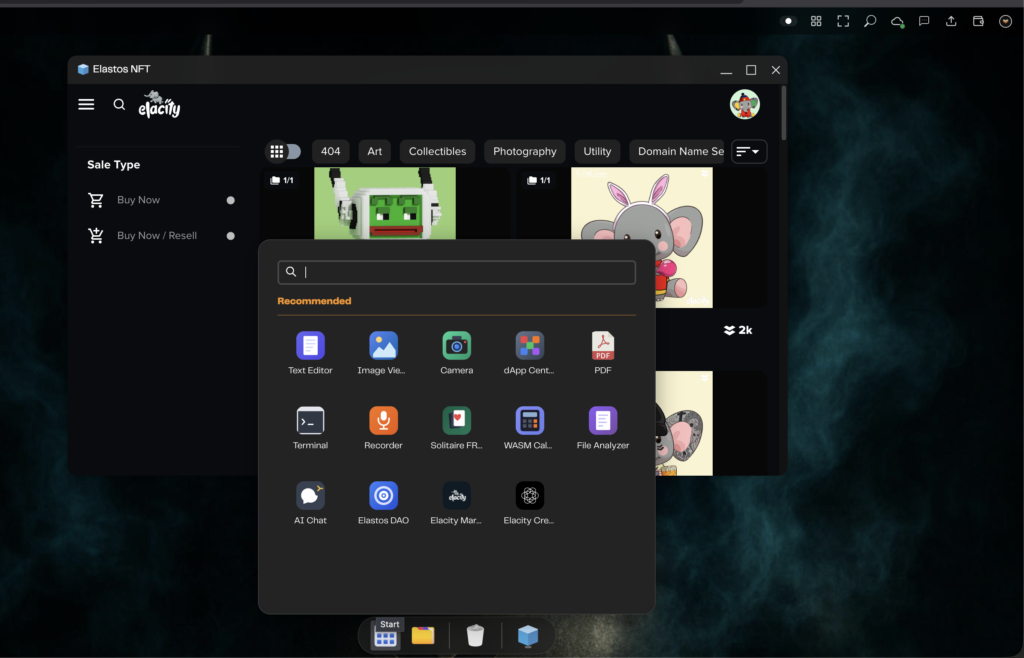
- Elastos NFT
- Glide Finance
Both supernodes, on two different dedicated server providers, now run Kubo and pin all six capsule CIDs. Public gateway checks through ipfs.io and Pinata confirmed that the apps are reachable globally through IPFS. This means any PC2 node should be able to fetch the v1.2 capsule packages from the network.
The dApp Centre was cleaned up too. The catalog went from 15 apps to 6 real apps, removing filler cards. Boot sync now installs only system apps by default, stale local entries are cleaned up, sidebar categories were improved, and icon fallbacks were added so broken images do not appear in the launcher.
An audio-only DASH playback bug was fixed as well. Some MP3 content packaged through Bento4 was stalling around 39 seconds. The fix changes audio-only playback to use sequence mode, which keeps the audio segments playing continuously. The fix applies to both encrypted DRM playback and clear DASH playback.
The runtime-player UI also received a visual pass. dDRM Viewer, Media Player, Creator, and Market now use a more consistent dark palette, so the apps feel like parts of the same product instead of separate tools.
3. Security Hardening Across PC2 and the Gateway
This was also a major security week.
An external security researcher submitted an 11-finding report on April 18. Seven findings belonged to the PC2 node and web gateway codebase, four belonged to the smart-contracts repo, and one was deferred because of low traffic risk. All seven in-scope PC2 and gateway findings were closed across four waves within roughly 36 hours.
The fixes covered mock-token access, unauthenticated install paths, Particle login hardening, setup wizard lockdown, gateway command execution risks, provisioning tokens, and secret scanning through gitleaks.
After the external report, the team ran an internal audit and found 21 more issues in similar areas. These included shell command risks, missing owner checks, cross-wallet data access, SSRF risks, weak file access links, scheduler risks, and upload path handling.
Another three hardening waves followed. In total, the team closed 20 of 21 internal audit findings. The remaining item is TLS pinning for the ESC RPC proxy, which is blocked on DNS access for elastossmartchain.ela.city, not by code work.
Several security patterns were applied across the codebase:
- Shell-string execution was replaced with safer argument-based process calls.
- Privileged routes now require owner access.
- Cross-wallet fallback paths were removed.
- Rate limits were added to sensitive forwarders.
- File access URLs now use HMAC signing.
- SSRF protections were added for private, local, and internal IP ranges.
- Secret scanning now runs before commits, in CI, and on push.
The security regression suite passed, with 79 cases across five specs. The file URL signer passed 12 functional cases, and the private-IP checks passed their test cases. This gives v1.2 a much stronger base before release.
4. Product, Explorer, Contracts, and Outreach Progress
Outside the core release work, several product and ecosystem tracks also moved forward.
The new Elastos blockchain explorer, already live at blockchain.elastos.io, continued in development with 200 new commits since it’s launch, adding new features that are crucial for chain analysis.
The smart-contract workstream also continued. The focus this week was moving ownership and fee recipient settings from the compromised Elacity user to a new user, reviewing the latest PC2 updates for compatibility, updating the Lit keystore service, checking sync behavior, and preparing clearer documentation for metadata standards and IPFS lookup.
The team also continued external outreach. The founder was on the ground at Google Cloud Next in Las Vegas, speaking with people around enterprise AI, cybersecurity, infrastructure, and data governance. The main themes were sovereign compute, security isolation, AI accountability, and tokenised data rights for autonomous AI agents.
This starts a broader four-week outreach run, with Bitcoin 2026, Consensus Miami, the Digital Asset Yield Summit, the DAT Summit, and the FT Digital Assets Summit also on the path.
The key message is becoming clearer: PC2, Runtime, Lit, and dDRM are not just separate pieces. Together, they point toward a user-controlled environment where data access, rights, payments, and software permissions can be enforced directly by the system.
5. A Community-Found P0 dDRM Vulnerability Was Closed
The most important security event of the week came from the community.
On April 17, a community member reproduced a P0 dDRM vulnerability during the v1.2 pre-release process. The older non-media Lit Action trusted a user address passed in by the caller. Because the Lit Action source was loaded from a public IPFS CID, someone running their own PC2 node could call the action with another authorised buyer’s address and receive the content encryption key. By April 21, the fix was live and verified across PDF, PNG, MP4, and MP3. The team chose a session-key delegation model. The buyer signs once per day with their wallet, authorising a device-bound key. After that, asset opens can be signed silently by the device key, so users do not get a wallet popup for every file.
This keeps the user experience close to what people liked: double-click to open content. At the same time, the Lit Action now re-checks the wallet delegation, the per-request signature, the action ID, timing, and access rights before releasing the content key.
The old exploit path now fails with session or signature errors. EIP-1271 support for smart accounts was also confirmed. The fix went from community report to end-to-end shipped in four days.
What’s Next
The next step is to complete the final release checks and move toward the v1.2.0 release.
After that, the focus shifts to making the release easier to adopt: clearer capsule creation tools, stronger installer security, better launch metrics, and the first concrete steps toward bringing PC2 capabilities into the Runtime.
The team will also continue preparing the next layer of infrastructure work, including stronger RPC security and cleaner upgrade paths for cloud-hosted PC2 nodes.
On the outreach side, the conference circuit continues with Bitcoin 2026, Consensus Miami, the Digital Asset Yield Summit, the DAT Summit, and the FT Digital Assets Summit in London.
Try ElastOS
- Desktop Launcher (Mac and Linux): Download Launcher
- Terminal Install (Mac/Linux): curl -fsSL https://raw.githubusercontent.com/Elacity/pc2.net/main/scripts/start-local.sh | bash
- Runtime Install: curl -fsSL https://raw.githubusercontent.com/nicosql/elastos-runtime/main/scripts/install.sh | bash
- NVIDIA Jetson: cd ~ && git clone https://github.com/Elacity/pc2.net.git && cd pc2.net && sudo bash scripts/install-arm.sh
- Docs: docs.elastos.net | GitHub: github.com/Elacity/pc2.net
- Network Map: map.ela.city | Portal: portal.ela.city
- DAO Proposal: Keystone Fund Mandate
- Shipping Report: GitHub Discussion #12