Last week was a week of public releases, product hardening, and important user-facing progress across the World Computer Initiative. In seven days, the team released ElastOS Runtime v0.1.2, brought the new Elastos blockchain explorer live, added EPUB ebook and CBZ comic support to the dDRM pipeline, closed several security gaps raised directly by the community, improved protected reading and key caching, added sovereign NFT pinning to PC2, cleaned up the Elastos NFT app, published the first clear PC2 to Runtime convergence map, and fully closed out macOS notarization.
What Shipped: The Big Picture
Nine major workstreams moved forward in a single sprint:
- ElastOS Runtime v0.1.2, a major Runtime release focused on identity, rooms, install flow, and operator control
- EPUB and CBZ Support, ebooks and comics now work through the dDRM pipeline from upload to protected viewing
- Security Sweep, community feedback directly led to recovery improvements, Docker safeguards, and viewer hardening
- Protected Reading Improvements, copy-paste lockdown and better reading modes landed in the same week
- Smarter Key Caching, lower repeated decryption cost and better owner control for protected content
- NFT IPFS Pinning, users can now keep their NFT assets reachable from their own PC2 node
- Elastos NFT App Cleanup, a proper build pipeline and major bundle reduction
- PC2 to Runtime Convergence Map, the first real migration inventory was published
- Elastos Blockchain Explorer, the full production stack is now live at blockchain.elastos.io
In parallel, macOS notarization was fully completed, the Contabo ESC RPC proxy was brought into the wider infrastructure path, and portal and technical documentation were expanded across recovery, publishing, and Runtime convergence.
1. ElastOS Runtime v0.1.2, Released This Week
The Runtime is the engine underneath everything. It is the part that turns the broader World Computer vision into something people can actually install and run. This week, Runtime v0.1.2 was released, and it marks one of the clearest steps yet toward making ElastOS feel like one connected system.
The release focused on four main areas, identity, rooms, operator control, and the install and release path.
Identity is now tied more directly to the device, which gives the system a stronger starting point and makes the different surfaces feel more consistent. Rooms also moved forward, with hosted browser access now working more cleanly as part of the Runtime experience instead of feeling like a separate experiment.
The operator path was also made clearer. Advanced controls now live in a more explicit lane, which makes the difference between regular user flows and owner or admin flows much easier to understand.
Just as important, the release path itself got cleaner. Setup, documentation, public install checks, and release packaging were all tightened so the version people install matches the version the team is actually describing.
- 18 commits on the review/0.1.2 line, covering identity, hosted rooms, operator flow, public install checks, and release cleanup
- ~96,000 lines of code across 17 capsules, continuing to grow the Runtime as the core execution layer for the system
- Device-backed identity and hosted rooms, making the installed experience feel more like one working system and less like separate parts
2. EPUB and CBZ Support, A New dDRM Content Class
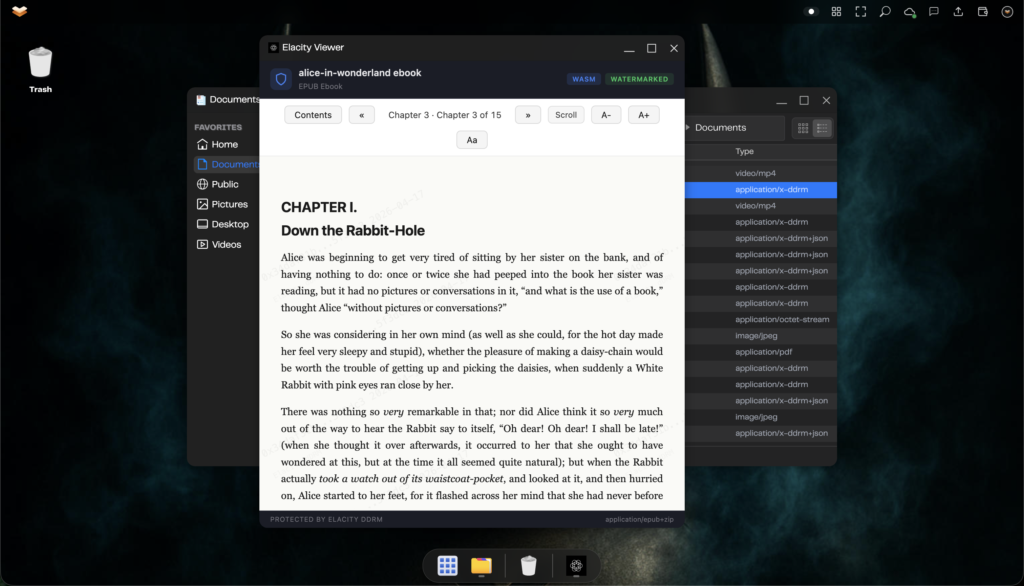
One of the biggest additions this week came from a simple community question, can PC2 protect ebooks the same way it protects other digital content?
This week, the answer became yes.
EPUB ebooks and CBZ comics are now supported through the dDRM pipeline from upload to protected viewing. That means creators can now work with a wider range of content types without needing a separate publishing path. Protected digital publishing on PC2 is no longer limited to the earlier content types. It now covers books and comics too.
3. Security Sweep, Driven by Community Feedback
This week’s security work was shaped directly by real user concerns.
The biggest addition was recovery. Users now have proper paths to restore identity from their recovery phrase, which means losing a volume no longer automatically means losing the identity tied to that setup.
The team also added clearer Docker safeguards so destructive commands are easier to spot before they wipe important data. Backups were separated more carefully as part of the same work.
At the same time, the new ebook and comic support triggered a broader hardening pass on the renderer itself. Size and safety limits were added so the new content flows are more resilient from the start.
- Mnemonic recovery added, users can now restore identity after losing Docker data
- Docker guard rails shipped, with clearer warnings and backup separation for safer operation
- Renderer hardening completed, closing multiple unsafe paths while the new content types were being added
4. Protected Reading, Stronger Lockdown and Better UX
This week, the reading surface was tightened so casual copy-paste extraction is much harder. The goal was not to pretend leaks are impossible, but to stop the easiest path and make the protection match the intent of the system more closely.
At the same time, the reading experience itself improved. The first version leaned too heavily toward chapter jumping when readers were expecting something closer to page-by-page reading. That gap was closed with better reading modes, giving users a more natural way to move through protected content.
Protected reading should still feel like reading, not like fighting the software.
- Copy-paste lockdown added, reducing casual text extraction from protected ebook views
- Paged and scrolling modes shipped, giving readers a more natural experience inside the DRM viewer
- Forensic watermarking retained, so leaked text still remains traceable
5. Smarter Key Caching, Lower Repeat Cost
Some of the most useful work this week happened behind the scenes.
The content key cache was audited and corrected so it now behaves the way it was supposed to. In simple terms, active readers are less likely to lose their place in the cache, which means fewer unnecessary repeat decrypt calls.
Owner controls were also added so cache state can be checked and cleared when needed, especially after access changes.
For users, the result is straightforward. Reading multi-chapter or multi-page protected content becomes cheaper and smoother because the system is no longer repeating work it should already remember.
6. NFT IPFS Pinning, Moving Ownership Closer to the User
Until now, NFT users still depended too much on Elacity’s gateway to keep their artwork and metadata reachable. If that path failed, the ownership remained on-chain, but the user experience around the asset could break.
This week, PC2 took a step toward fixing that.
Users can now pin their own NFT assets through their node, which means their collection can remain reachable from infrastructure they control. The app now exposes pinning more clearly, and users can see which assets are already preserved locally.
7. Elastos NFT App, Build Pipeline and Cleanup
The Elastos NFT app moved from a quick port toward something much cleaner this week.
A proper build pipeline was added so the app can be rebuilt consistently instead of relying on a manual process. At the same time, the app was stripped down to better match its actual role on Elastos Smart Chain.
Unused features and irrelevant sections were removed, the content views were tightened around what really exists on the chain, and the overall bundle size dropped sharply.
8. PC2 and Runtime Convergence, First Clear Map Published
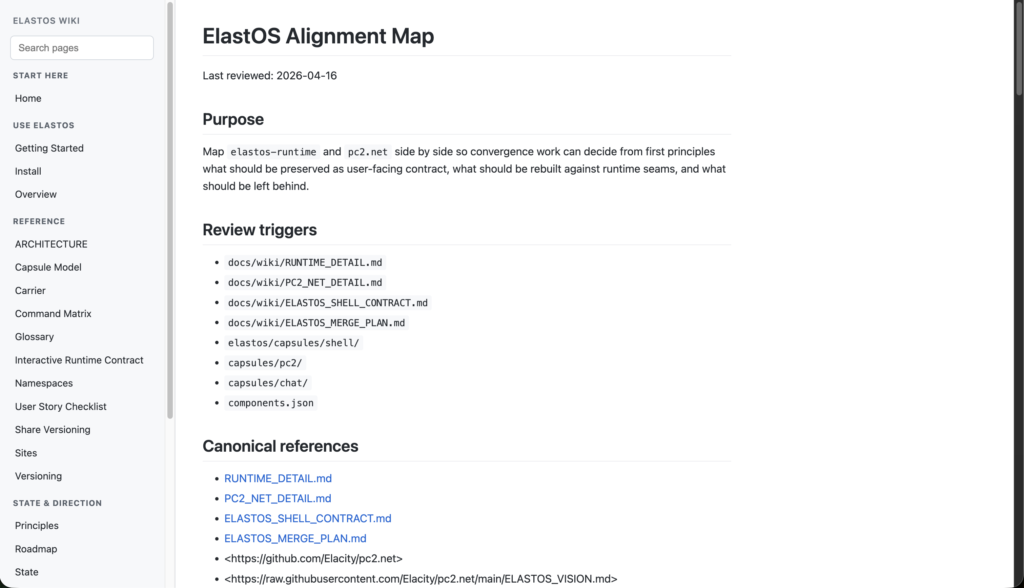
PC2 and the Runtime are meant to come together over time, but that only works if both sides share a clear view of what already exists and what should move first.
This week, that view was finally published.
The new convergence inventory lays out the main PC2 subsystems that can move toward the Runtime capsule model over time. More importantly, it frames the migration as a bottom-up sequence, not a giant rewrite.
That is the right approach. Instead of trying to replace everything at once, the plan is to move piece by piece, starting with the most ready areas first.
9. Elastos Blockchain Explorer, Now Live
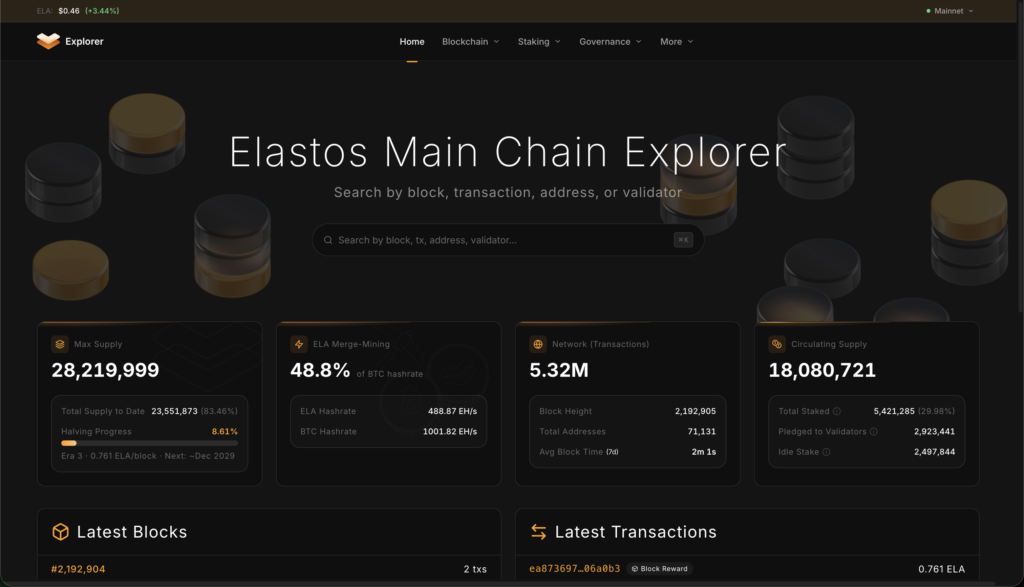
The new Elastos blockchain explorer is now live, and this was one of the biggest public-facing milestones of the week.
The Elastos ecosystem has needed a modern main chain explorer for a long time, something that goes beyond a simple block list and gives people a fuller view of transactions, addresses, governance, staking, and live chain activity.
That stack is now live.
The explorer was built end to end, from chain sync to database to API to frontend to monitoring. The result is a public tool that covers the full story of what is happening on the chain while also watching its own health in production.
This is not just a nicer interface. It is core infrastructure that the ecosystem can actually use.
- Full production explorer now live, covering blocks, transactions, addresses, governance, staking, charts, and mempool data
- Sub-millisecond balance lookups, powered by a 20 million entry UTXO cache
- Live monitoring and node cross-checking, with production health checks and operator alerting already in place
Infrastructure and Operations
macOS notarization is now fully complete. The installer path is much cleaner, and users can install through the normal DMG flow without extra workaround steps.
Other work this week included RPC proxy progress, gateway reliability fixes, asset handling cleanup, and development environment cleanup. None of that is flashy on its own, but together it reduces friction across both product and engineering work.
- All 6 Apple submissions accepted, fully closing the notarization process for the Mac installer
- A new ESC RPC proxy brought into the PC2 path, helping prepare infrastructure for future Runtime consumption
- Development environment cleaned up, including stale process removal and static asset handling fixes
Website and Portal Updates
Technical Documentation
- Recovery guide added
- Ebook publishing documentation updated
- dDRM integration notes expanded with cache and admin endpoint changes
- PC2 to Runtime convergence inventory published for handover and planning
What’s Next
- Manual QA for EPUB and CBZ support, including paged mode, copy-lockdown, natural-sort comics, and fixed-layout handling
- PC2 adoption of Runtime v0.1.2 capabilities, wiring the new identity and room surfaces into the broader PC2 experience
- Local-first upload path, reducing publish flow dependence on slower remote IPFS paths
- Market priority fixes, addressing the remaining transaction issues identified in the previous audit
- Fixed-layout EPUB fallback, so pre-paginated EPUBs can move more smoothly into the protected reading flow
- Runtime capsule migration begins, starting piece by piece from the convergence inventory
- NFT pinning Phase 8, moving toward automatic pin-on-buy for sovereign local preservation
- Conference circuit, Google Cloud Next, Bitcoin 2026, Consensus Miami, DAT Summit, and FT Digital Assets Summit across late April and May
Summary Statistics
- PC2 Engineering: 11 non-merge commits, 53 files touched, 8,418 insertions, 500 deletions
- ElastOS Runtime v0.1.2: 18 commits, 17 capsules, ~96K LOC
- New dDRM content class: EPUB and CBZ support added end to end
- Elastos NFT app: bundle reduced from 45 MB to 22 MB
- Blockchain explorer: full production stack live at blockchain.elastos.io
- macOS notarization: complete, with all 6 submissions accepted
Key Links This Week
- ElastOS Runtime v0.1.2: github.com/Elacity/elastos-runtime
- Elastos Blockchain Explorer: blockchain.elastos.io
- Install ElastOS Runtime: curl -fsSL https://elastos.elacitylabs.com/install.sh | bash